News
There is a shiny new data extraction method in the alpha of the new release. It uses WAITFOR-based injection (slow) and DNS tunnels (fast!!). It is still a bit experimental, but it could help you in your next penetration test. You can find it in the Download. Why we decided to add a data extraction module even if lots of other tools do that already? The answer is in the FAQ page.
Introduction
Fancy going from a SQL Injection on Microsoft SQL Server to a full GUI access on
the DB? Take a few new SQL Injection tricks, add a couple of remote shots in the registry to disable Data Execution Prevention, mix with a little Perl that automatically generates a debug script, put all this in a shaker with a Metasploit
wrapper, shake well and you have just one of the attack modules of sqlninja!
Sqlninja is a tool targeted to exploit SQL Injection vulnerabilities
on a web application that uses Microsoft SQL Server as its back-end.
Its main goal is to provide a remote access on the vulnerable DB server,
even in a very hostile environment. It should be used by penetration
testers to help and automate the process of taking over a DB Server
when a SQL Injection vulnerability has been discovered.
Plus, it also streams music!! (...kudos to sid77 and smiler for
being the first to spot the Easter Egg)
Have a look at the flash demo and then feel free
to download.
It is released under the GPLv3
Screenshots



Features
The full documentation can be found in the tarball and also here, but here's a list of what the Ninja does:
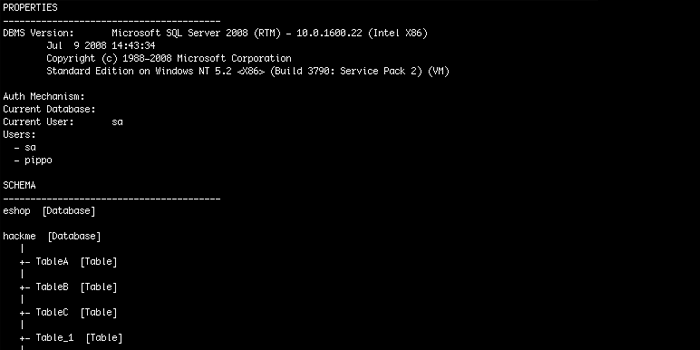
- Fingerprint of the remote SQL Server (version, user performing the queries, user privileges, xp_cmdshell availability, DB authentication mode)
- Data extraction, time-based or via a DNS tunnel
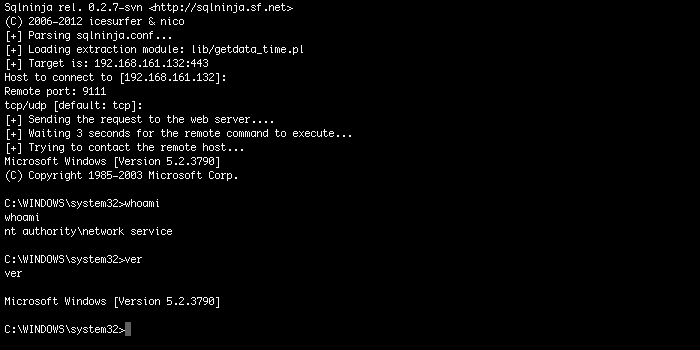
- Integration with Metasploit3, to obtain a graphical access to the remote DB server through a VNC server injection or just to upload Meterpreter
- Upload of executables using only normal HTTP requests (no FTP/TFTP needed), via vbscript or debug.exe
- Direct and reverse bindshell, both TCP and UDP
- DNS-tunneled pseudo-shell, when no TCP/UDP ports are available for a direct/reverse shell, but the DB server can resolve external hostnames
- ICMP-tunneled shell, when no TCP/UDP ports are available for a direct/reverse shell but the DB can ping your box
- Bruteforce of 'sa' password (in 2 flavors: dictionary-based and incremental)
- Privilege escalation to sysadmin group if 'sa' password has been found
- Creation of a custom xp_cmdshell if the original one has been removed
- TCP/UDP portscan from the target SQL Server to the attacking machine, in order to find a port that is allowed by the firewall of the target network and use it for a reverse shell
- Evasion techniques to confuse a few IDS/IPS/WAF
- Integration with churrasco.exe, to escalate privileges to SYSTEM on w2k3 via token kidnapping
- Support for CVE-2010-0232, to escalate the privileges of sqlservr.exe to SYSTEM
Platforms supported
Sqlninja is written in Perl and should run
on any UNIX based platform with a Perl interpreter, as long as all
needed modules have been installed. So far it has been successfully
tested on:
- Linux
- FreeBSD
- Mac OS X
- iOS
Sqlninja does not run on Windows and we are not planning a port in the near future
Contact
icesurfer
bio: I break things for a living
email: r00t .at. northernfortress .dot. net
PGP: 0x8388C385
Twitter: http://twitter.com/icesurfer
nico
bio: just a German and world citizen
email: nico .at. leidecker .dot. info
